Cyber security for your business
Managed Security Service Provider (MSSP)
When evaluating a managed cyber security solution for your business it can be hard to know what a modern business needs to stay cyber security safe and even what a modern cyber security “posture” is. A free consultation with a member of our team is usually the best first step.


Cyber Security Readiness
It’s easy to think that if your business hasn’t yet been targeted by a cyber attack that it won’t happen to you and that spending money on security measures for you and your team would be a waste of capital.
But speak to anyone that has just become the subject of a cyber attack and they will tell you they wish they’d done something sooner and that protecting your business is imperative. Because it’s not just you and your team that’s affected it’s likely your clients will be too.
All the emails alone that you hold from your clients give valuable clues as to their company structures and email addresses making them the next target for hackers.
Once they are in your systems and data they will see who you work with and target them too, further damaging your company’s reputation.
You have a duty of care not just to your team but your clients too, to put sufficient cybersecurity measures in place.
They all benefit from proactive IT support




Full-stack security
First things first, getting to the nuts and bolts.
As I’m sure you are aware IT is an extremely fast moving sector, and cybersecurity and associated threats are ever on the increase.
Protecting your business from attack is never 100% guaranteed.
Governments and large corporations are breached frequently by bad actors. Governments and large corporations spend millions a year on cybersecurity and still are breached at times.
We work with you and your team to protect your data and make it harder for an attack to be successful by using industry-standard cybersecurity software and our team’s knowledge.
Running a secure, efficent and productive business and allowing your team to collaborte and produce results relys on having the technology and tools available to achieve those results.
With the right IT partner, we can help you remove IT frustrations, save your business money and time with managed IT services, network solutions and modern software.
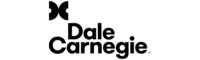
I’m sure you’re aware of the need for an “Internet security” or “Anti Virus” package on your devices to protect against a cyber security issue. But these really are the first step, we offer full-stack security to prevent issues from start to finish.
Managed security as a service means that not only are we taking care of your businesses I.T. day to day operations and making sure things are running efficiently but also keeping a professional and proactive eye on outside threats to your business and implimenting the most up to date cyber security protections.
We don’t just have industry-leading software in our product stack but we have real human beings proactively monitoring your data and devices.

Managed Detection and Response (MDR)
Managed Detection and Response (MDR) is a comprehensive cybersecurity service that leverages a mix of technology and human expertise to detect, analyze, and respond to threats in real-time. It’s like a vigilant, 24/7 security team for your network.
If, for instance, Tim in HR unwittingly downloads a malicious file, MDR systems would immediately identify the unusual activity. The threat is then analyzed by our ThreatOps team, who determine the nature and severity of the threat, which could range from spyware to ransomware.
Once the threat is evaluated, the compromised host is isolated within moments, curtailing the spread of the threat across your network. Meanwhile, our security team is addressing the issue and working on its resolution. The host is automatically released when the threat is neutralized, or it can be manually released if necessary.
This proactive approach to cybersecurity ensures that your business continues to operate safely and without disruption, complementing automated systems with human analysis to give you the best possible defense against cyber threats.
Penetration Testing
Penetration testing, or pen testing as it’s often called, is a proactive and crucial method to safeguard your business’ digital assets. In the unceasingly dynamic landscape of IT, pen testing offers a unique and strategic approach to cybersecurity by simulating cyberattacks on your own systems. Why? To exploit any vulnerabilities before a malicious actor does.
Your internet connected systems are therefore a target for hackers and many SMEs are seen as “low hanging fruit”. Governments and large corporations, despite allocating vast resources to cybersecurity, frequently fall victim to such threats. It’s a stark reminder that no entity is immune, regardless of its size or the scale of its cybersecurity budget.
You should therefore take your cybersecurity seriously and penetration testing should be high on your list because it equips you with the knowledge of where and how a cyberattacker might breach your systems. It’s like a regular health check-up for your business’ digital infrastructure, providing an insight into your cybersecurity defenses’ real-world effectiveness. And should be carried out yearly.
However, pen testing is not a standalone solution. It’s the starting point of a comprehensive, full-stack security service. While it’s imperative to have fundamental measures like Internet security packages and Anti-virus software, these are merely the initial steps on the cybersecurity ladder.
We adopt a multilayered approach to protect your data. We combine top-tier cybersecurity software with our team’s expertise to make your digital fortress as impenetrable as possible. We strive to make it harder for a cyberattack to be successful and to minimize its impact if it does occur.
By working with us, you’re choosing more than just an IT partner. You’re opting for a team that alleviates IT frustrations, improves efficiency, and provides innovative network solutions. Our goal is to save you valuable time and resources while allowing your team to collaborate and produce results effectively.
Moreover, our managed security as a service encompasses not just day-to-day IT operations. We vigilantly monitor the evolving threat landscape and update your cybersecurity measures accordingly. Our approach is not just about having the best software; we also have real people—experts who monitor your data and systems proactively.

Endpoint Detection and Response (EDR)
Endpoint Detection and Response (EDR) is a security solution designed to protect your devices from cyber threats, enabling detailed visibility and control over activities at the endpoint level.
Let’s say Sam from the design team accidentally opens a malicious attachment—EDR technology identifies this unusual behavior and triggers an alert. Our expert ThreatOps team then assesses the threat, which could be anything from a rapidly-spreading worm like Emotet or Trickbot to ransomware or remote access tools.
Post threat evaluation, EDR swiftly isolates Sam’s machine, preventing the malware from propagating through your network, and begins remediation processes. The host will be sequestered within moments of the incident report generated by the threat analyst.
Once the incident is fully resolved, Sam’s device is automatically brought back into the network fold, or it can be manually reintegrated earlier if necessary. This blend of automated detection, expert human analysis, and prompt response ensures the utmost protection for your organization from burgeoning cyber threats.
How we can help your Business
Weekly checks.
We perform weekly internal checks to make sure there’s no risky logins, we check user login locations to make sure they are from your location (or there’s a good reason for a foreign logins), new rules created for mailboxes etc.
These checks help keep you and your business data safe from fraud and cyber security breaches.
Microsoft 365.
If your business isn’t already using Microsoft 365 for emails we would seriously recommend it, we can manage the migration so you have zero downtime.
The extra security, protection, and auditing capabilities just might protect the future of your business. Microsoft 365 allows our team to keep your data protected from cyber security attacks.
Dark Web Monitoring.
Companies offering dark web monitoring is a bit like Snake Oil, the nature of the dark web is that it’s hidden and nefarious.
So when we say dark web monitoring let’s be clear.
We will monitor your company emails and account credentials in known illicit dark web shops and known data breaches.
Multi Factor Authentication.
Possibly the best way to thwart many cyber security incidents is to enable multi factor authentication on your business accounts.
This generates a code for each login that is delivered to an app or a mobile phone via SMS.
Penetration tests.
We provide resiliance testing for your network and it’s devices. This way we can find weak points and likely points of entry for a cybersecurity attack.
Blocking these ports and points of entry will help keep your business on the right side of a cyber security incident.
Future proofing.
We will look at your network and how you use your devices each month to make sure we’re moving your business with the times and avoiding a cyber security attack.
IT & Cyber Security Services
Protecting your business from attack is imperative to not only your continued success but your whole companies survival.
If you’re not properly prepared and your organisation succumbs to a cyber security incident if you do survive you’re starting from scratch in most cases, with zero reputation and zero data.
It’s not a nice place to be, get protection before it’s too late.

Cyber Security Essentials & Cyber Security Essentials Plus
The Cyber Essentials accreditation is part of a drive to get the UK protected from cyber threats by the Government. The scheme Cyber Essentials is a set of controls that determine if a business is adequately protecting itself from cyber threats.
Items checked by the Cyber essentials scheme include:
- Is Autorun/Autoplay disabled on all company workstations.
- Are employees using standard user level accounts and not admin level accounts.
- Is Antivirus/Internet security installed on all workstations.
- Are all operating systems patched within 14 days of a critical update or security fix being released.
Cyber Essentials has two options, firstly a basic certification that asks a set of questions the business needs to answer. Once marked you business will recieve the Cyber essentials basic certification.
The second option is Cyber Essentials Plus. To obtain Cyber Essentials Plus the business must first reach Cyber Essentials Basic certification within the last three months. Then an onsite audit must be carried out to check that all of the elements from the self-assessment are being put into practice.


MDR security
Everyone loves an acronym.
MDR stands for Managed detection and response (MDR) an MDR solution identifies active threats and allows us to quickly respond to eliminate, investigate or quarantine them.
Using a combination of sophisticated cybersecurity software protection and human expertise to monitor your business environment, discover emerging and active threats and then respond accordingly.
Managed detection and response significantly reduces the time taken for businesses to detect cybersecurity threats and compromised devices.
Studies have found that it takes most businesses as much as 206 days to identify a security breach, by using a managed detection and response solution cybersecurity threat detection and remediation can take just a few hours.
Our delighted customers
Darren and the team at Aurora are both knowledgeable, professional and put the needs of me and my business first.
Regardless of the issue, they have been quick to respond and just as quick to resolve.
Highly recommended.
Fantastic Personal Service! Darren Dealt with my IT Issues with urgency and efficiency. Highly Recommended!
A breath of fresh air when it comes to IT support. Recently turned to Aurora moving from our previous provider. Completely understood what we required and it wasn’t like talking to a know it all brick wall. Made everything simple to understand, slick and more importantly easy to use! Thanks Darren and team.
We would highly recommend Aurora Tech Support to anyone who is looking for good IT support whatever the problem. Darren has assisted us with all our IT issues and always been on call first hand when required. We look forward to working with you in the future.
Great service: really helpful and quick to resolve my difficulty. I’d definitely recommend Aurora. Thank you




